Welcome! If you're new to information security, things might feel overwhelming at first. There's a sea of acronyms, laws, frameworks, and standards — but don't worry. Let's break it down.
Why Does Security Matter?#
Everything starts with information security. In today's digital world, information is one of the most valuable assets — and also one of the most vulnerable.
So, what is Information Security?#
Information Security means protecting data from:
- Unauthorized access (someone reads it who shouldn't)
- Alteration (data gets changed maliciously or accidentally)
- Destruction or loss (data gets deleted or lost)
We use the CIA Triad to remember its 3 main goals:
- Confidentiality: Keeping data secret.
- Integrity: Ensuring data is accurate and unaltered.
- Availability: Making sure systems and data are accessible when needed.
Example: If your company handles payment information and it gets leaked or tampered with — you've failed one or more parts of the CIA triad.
Wait… What's With All the Terms?#
When you start working in this space, you'll hear words like "framework," "standard," "policy," "controls," and "guidelines" all the time.
They sound similar but serve different purposes:
Policy
A policy is a high-level rule or statement of intent that defines what an organization must do to protect information and operate responsibly.
Purpose: To set the direction and expectations. It doesn't get into the how — just the what and why.
Example:
"All employees must use multi-factor authentication to access corporate systems."
Think of it as: The organization's internal law — set by leadership.
Standard
A standard is a mandatory specification that supports a policy. It provides the specific requirements (often technical or operational) that must be followed.
Purpose: To ensure consistency and uniformity in implementation across the organization.
Example:
"Passwords must be at least 12 characters and include a mix of upper/lowercase, numbers, and symbols."
Think of it as: The "rulebook" that tells you how to follow the policy.
Guideline
A guideline is a recommended (not required) practice. It offers helpful advice or suggestions to improve security or compliance.
Purpose: To provide flexibility. It's ideal for situations where you need professional judgment or when strict rules might not apply.
Example:
"It's recommended to lock your workstation when stepping away, even if it's for a short break."
Procedure
A procedure is a step-by-step instruction that tells you exactly how to carry out a task or process in alignment with a policy or standard.
Purpose: To provide detailed instructions to execute tasks safely and consistently.
Example:
"To reset your password, go to the intranet portal → Click on 'Account Settings' → Select 'Change Password' → Enter old and new password → Click Submit."
Framework
A framework is a structured set of rules, best practices, controls, and guidance that helps organizations manage security, risk, or compliance. It may include policies, standards, controls, and more.
Purpose: To provide a comprehensive blueprint for managing information security or compliance programs.
Example Frameworks:
- ISO 27001 — Information Security Management
- NIST 800–53 — Technical controls for federal systems
- SOC 2 — Trust principles for service organizations
A blueprint or architecture for building your entire security program.
Regulation
A regulation is a legal requirement issued by a government or authority that organizations must comply with. Non-compliance can lead to legal penalties, fines, or bans.
Purpose: To protect individuals' rights, especially around privacy, financial data, or healthcare.
Examples of Regulations:
- GDPR (EU data protection)
- HIPAA (US health data privacy)
- CCPA (California Consumer Privacy Act)
- FISMA (US federal systems)
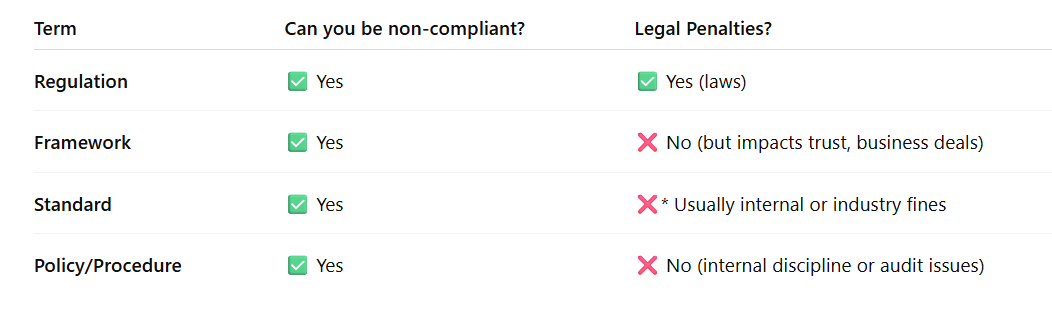
Can a company be "compliant" or "non-compliant" just by following regulations — or does this also apply to frameworks, policies, etc.?
Yes, a company can be compliant or non-compliant with:
- Regulations (e.g., GDPR, HIPAA)
- Standards (e.g., ISO 27001, PCI DSS)
- Frameworks (e.g., NIST 800–53, SOC 2)
- Its own internal policies or procedures
But the meaning and consequences of non-compliance depend on what you're failing to follow:
| Type | Compliance With It Means… |
|---|---|
| Regulation | You are following the law. |
| Framework | You are following an industry-recognized structure. |
| Standard | You are meeting defined technical or procedural requirements. |
| Policy | You are following your own organization's internal rules. |
Does non-compliance always lead to legal penalties or fines?
Only regulations can lead to legal penalties (e.g., fines, bans). For everything else — the consequence is business or internal impact, not legal punishment.
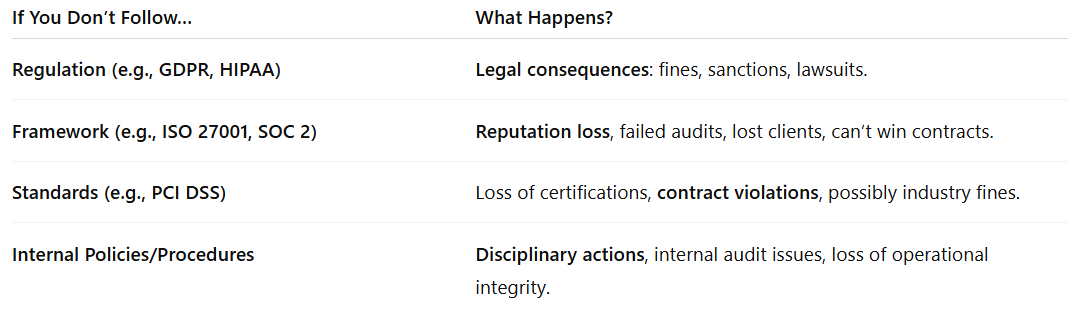
- Non-compliance with GDPR → You might be fined €20 million or 4% of annual revenue.
- Non-compliance with ISO 27001 → You may lose your ISO certification and fail a client audit.
- Non-compliance with internal policy → Your CISO might escalate the issue; you might face internal consequences.
- Non-compliance with PCI DSS (for credit card data) → You might lose the ability to process cards or face fines from card networks.
- HiTrust CSF — A unified framework mapping multiple standards (HIPAA, ISO, NIST)