Want to understand how ISO 27001 certification actually works? Great — let's simplify it.
In this article, I will be talking about:
- Introduction to ISO 27001
- Why do companies even need ISO 27001
- How does it work?
- How Does the Certification Process Actually Happen?
- Statement of Applicability (SoA)
Think of ISO 27001 as a global benchmark designed to help organizations protect their information before breaches, disasters, or costly mistakes happen. In simpler terms, it's like building a solid fence around your most valuable information.
Why Do Companies Even Need ISO 27001?#
With so many standards out there, you might wonder — why ISO 27001 specifically? Well, consider these facts:
- In 2023, there were around 2,361 cyberattacks daily.
- 83% of companies experienced at least one cybersecurity breach.
- GDPR fines alone can reach up to €20 million or 4% of annual revenue (ahhh, that's a lot of money), whichever is higher.
Given these risks, ISO 27001 becomes a lifesaver — it helps companies prevent breaches and stay secure.
Don't worry about the large number "27001" — ISO covers various standards like food safety (ISO 22000) and quality management (ISO 9001) as well. ISO 27001 specifically deals with information security management.
How Does ISO 27001 Work?#
1. Main Clauses (The Big Picture Rules)#
ISO 27001 has 10 clauses, but you'll mostly hear about clauses 4 through 10:
- Clause 4: Understanding your organization and its security risks.
- Clause 5: Ensuring top management actively supports security efforts — it's not just an IT issue.
- Clause 6: Planning your information security objectives and strategies.
- Clause 7: Providing necessary resources, training, and communication about security.
- Clause 8: Implementing security processes and controls.
- Clause 9: Monitoring, measuring, and reviewing the effectiveness of your security measures.
- Clause 10: Continuously improving your information security management system.
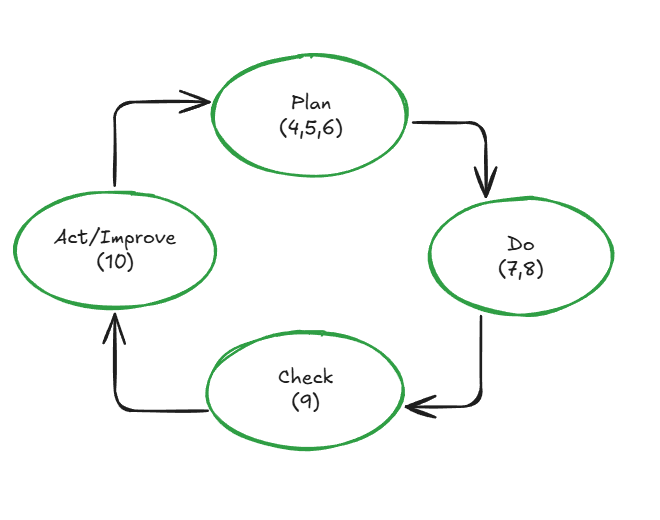
ISO 27001 follows the continuous improvement cycle: Plan → Do → Check → Act (Improve). It's not something you set up once; you continuously monitor and enhance it.
2. Annex A (Think: The Detailed Checklist)#
Annex A provides a checklist of 93 security controls that companies implement practically. Example controls include:
- Using strong passwords (Access Control)
- Encrypting sensitive data (Cryptography)
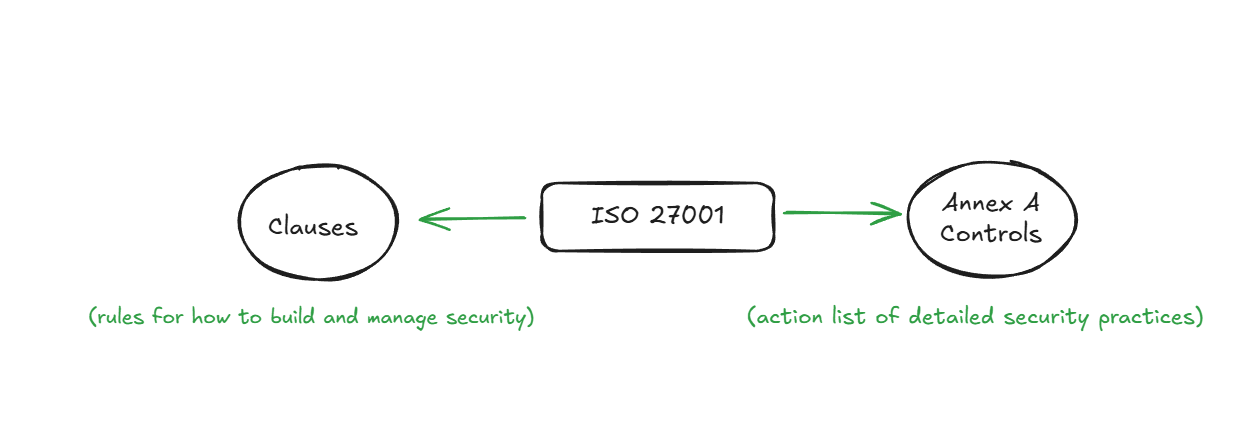
What's the Difference Between Clauses and Annex A?
Imagine a bank identifying a risk, such as, "What if hackers steal customer credit card data?"
Clauses require the bank to first identify and evaluate this risk, then plan appropriate controls to mitigate it.
Annex A then gives specific actions to address this risk, such as encrypting databases or enhancing firewall protection.
Simply put:
Clauses: Force companies to think, plan, and strategize security.
Annex A: Offers practical solutions to execute those strategies.
How Does the Certification Process Actually Happen?#
Let me walk you through how ISO 27001 certification unfolds — this isn't theory; it's something I've personally experienced at work.
-
Build the ISMS: The company creates an Information Security Management System (ISMS). Think of it as building the engine for your security system — risk management, policies, controls, everything in one place. This phase typically takes several months and involves intensive planning and setup.
-
Employee Training and Awareness: Employees are trained on security practices, including managing strong passwords, recognizing phishing attempts, and understanding data protection responsibilities. Regular training sessions help ensure everyone is on the same page.
-
Internal Audit: Next comes an internal review to spot any gaps and fix them. I've seen teams thoroughly checking documents, testing access controls, updating policies, and adjusting practices based on feedback. This usually takes a few weeks to months depending on company size.
-
External Audit: A certified external auditor then formally reviews everything — not just paperwork, but actual conversations with employees, log reviews, and practical tests. This external audit generally lasts anywhere from a few days to several weeks.
-
Certification Awarded: If everything checks out, the organization receives ISO 27001 certification, valid for three years. But it doesn't end there — annual surveillance audits ensure ongoing compliance and continuous improvement.
Experiencing this firsthand showed me that ISO 27001 certification isn't just about ticking boxes. It involves thorough planning, teamwork, and an ongoing commitment to improving security. It's more than a task — it's a mindset.
Beyond just avoiding fines and breaches, ISO 27001 certification brings real business value:
- Builds trust with customers, partners, and investors who want to know their data is in safe hands.
- Opens doors to bigger contracts, especially with governments and enterprises that require certified vendors.
- Demonstrates professionalism and maturity in how your company manages sensitive information.
- Improves internal processes, ensuring security isn't an afterthought but part of your day-to-day operations.
- Supports legal and regulatory compliance, making audits smoother and reducing business risk.
So, it's not just about avoiding penalties — it's about showing the world that your organization takes information security seriously, and is committed to doing it right.
Does Being ISO 27001 Certified Mean You're Fully Secure?#
Not exactly — and this is an important point.
ISO 27001 certification doesn't guarantee perfect security. Instead, it means the company has built a systematic, risk-based approach to managing information security through policies, processes, training, and controls. It shows the company is serious about security and follows best practices, but it doesn't mean there are zero vulnerabilities or that nothing can go wrong.
Think of it like this:
A certified building has followed all fire safety regulations, but that doesn't mean a fire can't happen. It just means the risks have been assessed and preventive measures are in place.
That's why clients and partners often go one level deeper… let's understand that.
Statement of Applicability (SoA)#
One of the most powerful documents in ISO 27001 is the Statement of Applicability (SoA). It's a required part of the certification and acts like a security control checklist.
Here's what it includes:
- A list of 93 security controls from Annex A of ISO 27001
- Whether each control is applicable to the organization
- Whether it is implemented
- A justification for including or excluding each control
- A link to the organization's risk assessment
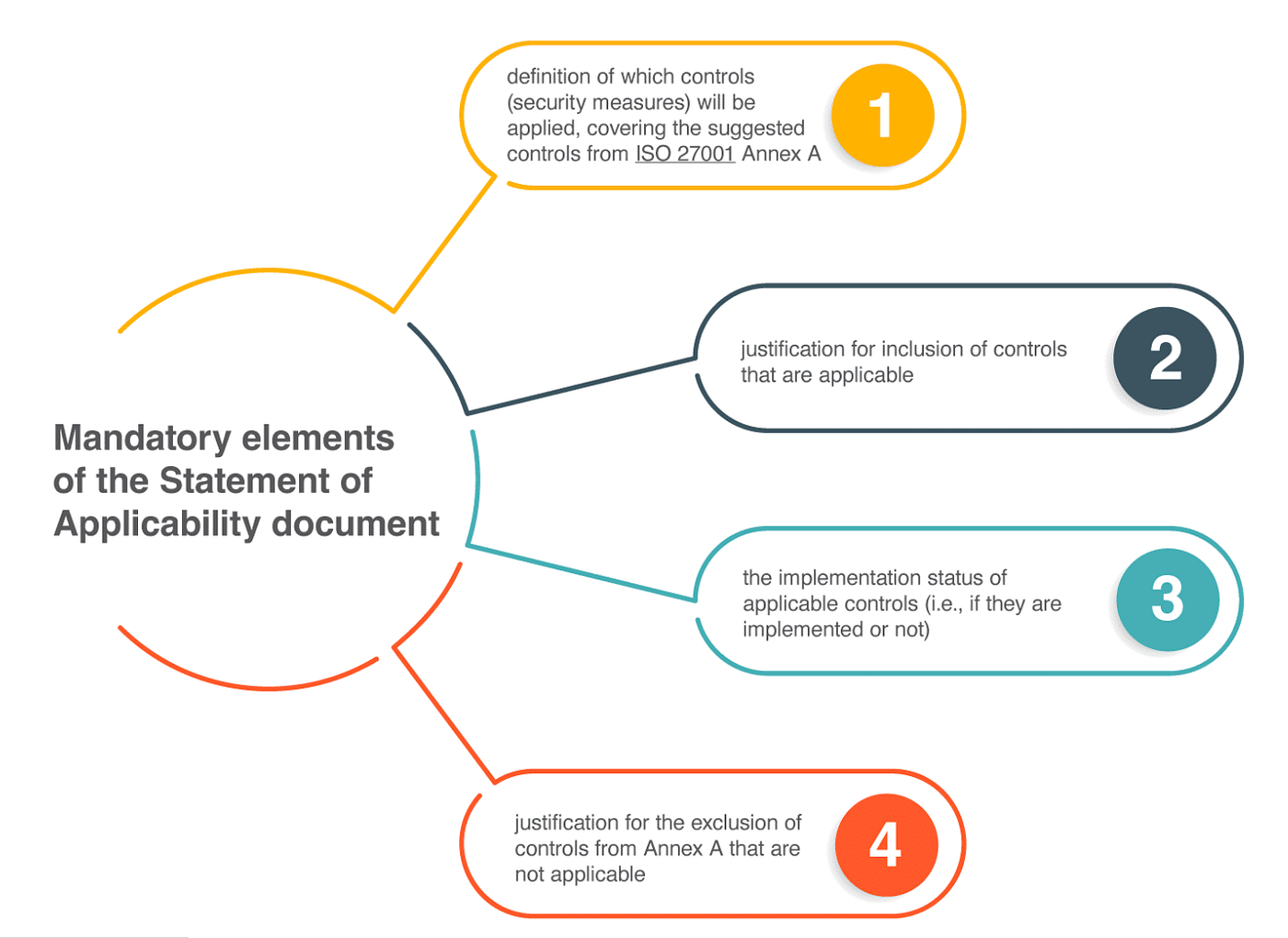
Why is this helpful?
→Because it tells you exactly what security measures are in place, what's not included, and why.
For example:
If a company excludes data encryption, the Statement of Applicability(SOA) must clearly state why. If they include access controls, the SoA explains how those are implemented and monitored.
This document gives customers and auditors transparency and confidence in how risks are being managed.
An organization having ISO 27001 is a strong sign of security maturity. But the due diligence often goes beyond the certification. Reviewing the Statement of Applicability (SoA) helps you understand the depth and relevance of the controls in place and whether they align with your security needs.